×Close
Security News
The words of Thomas Bossert, President Donald Trump's top cybersecurity adviser, boldly pledging to outdo previous administrations on improving federal government cybersecurity lead the latest edition of the ISMG Security Report.
Also in the Security Report, you'll hear (click on player beneath image to listen):
The ISMG Security Report appears on this and other ISMG websites on Tuesdays and Fridays. Check out our May 9 and May 12 reports that respectively analyze the maturation of cybercrime and how awareness programs fit in cyberdefense strategies.
The next ISMG Security Report will be posted on Friday, May 19.
Theme music for the ISMG Security Report is by Ithaca Audio under a Creative Commons license.
Business Continuity/Disaster Recovery , Governance , Ransomware
Ransomware: Your Money or Your Life 9 Ransomware Defenses Thwart Cybercrime Scoundrels Brian Honan talks ransomware at the AppSec Europe 2017 conference May 11 in Belfast, Northern Ireland. (Photo: Mathew J. Schwartz)
Brian Honan talks ransomware at the AppSec Europe 2017 conference May 11 in Belfast, Northern Ireland. (Photo: Mathew J. Schwartz)Criminals have been separating people from their possessions since possessions were first invented.
So for anyone who follows ransomware, the emergence of the WannaCry outbreak - aka WCry, WannaCrypt - Friday won't come as a shock.
True, the attack's efficacy has been enhanced by attackers marrying their crypto-locking code with a worm, allowing it to spread more easily. But these small innovations are designed with a clear purpose: to allow them to more easily steal more money from victims.
In other words, what's old is new again, now in cyber-enabled form.
The advice for blocking these attacks is simple: Spend time and money on proper prevention, or else you may be forced into considering whether it makes business sense to pay a ransom when attempting to recover from a ransomware infection. Even then, however, there's no guarantee that the criminals that have infected your systems will bother giving you a decryption key.
 Jeremiah Grossman highlights some of the many different faces of ransomware May 12 in a presentation at the AppSec Europe 2017 conference.
Jeremiah Grossman highlights some of the many different faces of ransomware May 12 in a presentation at the AppSec Europe 2017 conference.Brian Honan, a Dublin-based information security consultant who founded Ireland's first computer emergency response team - IRISSCERT - warns that there's no silver bullet for fixing ransomware. In an interview at last week's AppSec Europe 2017 conference in Belfast, Northern Ireland, he told me that too often, organizations' poor information security practices are partially to blame for their failure to prevent security incidents, including ransomware outbreaks, notwithstanding whatever tools they may have purchased.
"We go into numerous companies that have put in security technologies, but failed to configure them properly," Honan told me. "Why? 'Oh, we ran out of time,' they say."
9 Essential Ransomware Defenses
The basics of battling crypto-locking ransomware haven't changed of late. In the case of WannaCry, the ransomware can be spread via a worm that targets an SMB flaw in Windows, which all organizations should have fixed now regardless (see 5 Emergency Mitigation Strategies to Combat WannaCry Outbreak).
Following the WannaCry outbreak, the U.S. Computer Emergency Response Team - part of the Department of Homeland Security - has reiterated its advice for combating ransomware, as have multiple security experts.
Here's my summary of the experts' recommendations:
Maintain backups: Whitelist applications: Update and patch: Use anti-virus: Think 'least privilege': Kill email-borne macros: Don't click: Virtualize: Consider creating systems that use fast system recovery, via virtualization, to better respond to any malware outbreak. For example, Grossman says he knows of a New York bank that uses thin-client desktops running virtual machines. "Anytime they think there's an infection, they just reset" the virtual image running on all clients, he said. Work with law enforcement: "We're going to need help from law enforcement to investigate and arrest ransomware gangs," Grossman said (see FBI to Ransomware Victims: Please Come Forward).Scant Honor Among Thieves
Reminder: there's no guarantee that any individual or organization that does pay a ransom will ever receive the promised decryption key.
DO NOT PAY the ransom for WCRY, a manual human operator must activate decryption from the Tor C2. See screenshots, I've tried to hack it... pic.twitter.com/xzbK8eqw3Q
Security experts, including the researcher known as "Hacker Fantastic," say that's especially true for WannaCry. Many ransomware campaigns now use automated tools to receive bitcoin payments and send decryption keys to victims. But WannaCry's operators only have a manual process in place. As a result, computer science professor Alan Woodward at the University of Surrey tells me, it's likely that the attackers have no intention to trade decryption keys for ransom payments.
That's why the best, simplest and most effective advice remains: Prepare to battle ransomware outbreaks, or else prepare to pay the consequences.
Anti-Malware , Cybersecurity , Risk Management
Spain's Telefonica, England's NHS Are Among the Victims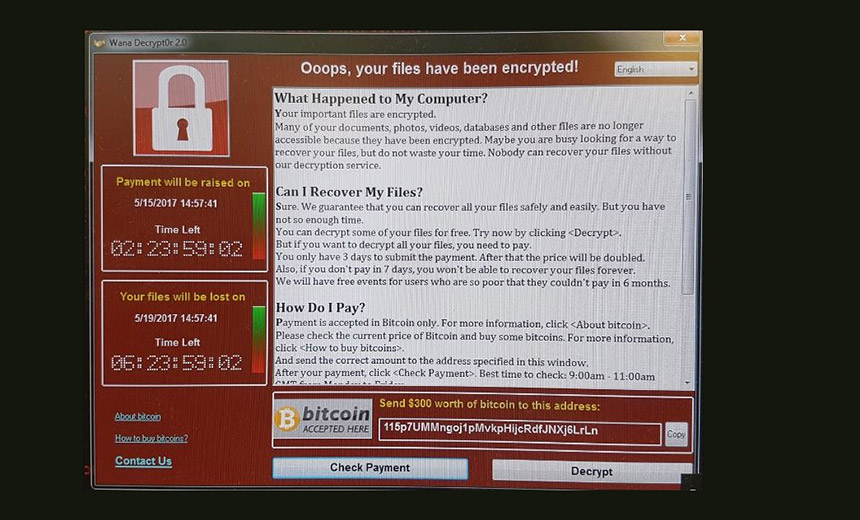 The lockscreen displayed by the WannaCry crypto-locking ransomware used in the attacks. (Source: Lawrence Dunhill)
The lockscreen displayed by the WannaCry crypto-locking ransomware used in the attacks. (Source: Lawrence Dunhill)This story has been updated.
See Also: 2017 Predictions on Data Security: Insights on Important Trends in Security for the Banking Industry
Spanish telecommunications giant Telefonica has reportedly instructed all employees to power down their systems in the wake of a massive ransomware attack. In addition, multiple National Health Service trusts in Britain say they've been hit with ransomware.
The Telefonica and NHS incidents appear to be part of a mass ransomware outbreak that has hit numerous organizations and institutions, reportedly ranging from Fedex to Russia's interior ministry. Researchers at Avast claimed that the attacks had spread to 99 nations. Multiple organizations have deactivated all endpoints as a precautionary measure.
The attacks against Telefonica and the NSH have infected endpoints with the WannaCry crypto-locking ransomware, which is also known as WCry and WanaCrypt0r.
Three security professionals with access to details surrounding the Telefonica incident say that attackers penetrated Telefonica's network - after which they deployed the WannaCry ransomware - by using the DoublePulsar "Equation Group" exploit leaked in April by the Shadow Brokers (see DoublePulsar Pwnage: Attackers Tap Equation Group Exploit).
The Shadow Brokers is the shadowy group believed to tie to the Russia government, while the Equation Group appears to be the National Security Agency's in-house hacking team, known as Tailored Access Operations.
Telefonica couldn't be immediately reached for comment.
DoublePulsar is an exploit that was patched in April by Microsoft in the form of MS17-010. That security update patches a server message block, or SMB, server vulnerability present in every Windows operating system from XP to Server 2008 R2, and which appears to have been used by the Equation Group to gain access to targeted networks, at which point additional attack tools could be deployed.
Avast reports that more than 75,000 related outbreaks of what it dubs "WanaCrypt0r 2.0" were seen across 99 countries on May 12.
 Map showing the countries most targeted by the WCry 2.0 outbreak. (Source: Avast)
Map showing the countries most targeted by the WCry 2.0 outbreak. (Source: Avast)NHS: Major Emergencies Declared
Security experts have confirmed that the SMB flaw was also used to penetrate multiple NHS networks, after which WannaCry ransomware was deployed, seemingly via automated attacks.
The British government says 48 NHS trusts in England have been hit by ransomware infections, leading the organizations in some cases to declare major emergencies and redirect patients - including to accident and emergency departments - to other locations. In addition, 13 of Scotland's 14 health boards were also hit by the ransomware, as were many doctors' practices in England and Scotland.
Colchester General Hospital, for example, has shut down all computer systems as a precautionary measure, Sky News reports, and issued a statement saying it was "postponing all non-urgent activity for today and we are asking people not to come to A&E."
Britain's national fraud and cyber reporting center, ActionFraud, confirms that multiple NHS trusts and hospitals - in London, Nottingham, Blackburn, Cumbria and Hertfordshire - have been hit in the attacks. Infected endpoints are demanding $300 in bitcoins, it says, adding that intelligence agency GCHQ's National Cyber Security Center is aware of the incident and working with the NHS and the National Crime Agency's National Cyber Crime Unit.
NHS computers have been locked by Wanna Decryptor #ransomware. To protect yourself in the future, follow our advice https://t.co/DVtbNKSk7X
"The investigation is at an early stage but we believe the malware variant is Wanna decryptor," an NHS Digital spokeswoman says. "NHS Digital is working closely with the NCSC, the Department of Health and NHS England to support affected organizations and to recommend appropriate mitigations. This attack was not specifically targeted at the NHS and is affecting organizations from across a range of sectors."
The ActionFraud alert also included a copy of this tweet by journalist Lawrence Dunhill:
Here's the malware attack which appears to have hit NHS hospitals right across England today pic.twitter.com/zIAJ6wbAG5
Alerts Issued in U.S.
Two U.S. agencies issued alerts about the worldwide ransomware attack on May 12.
The U.S. Department of Health and Human Services notes: "HHS is aware of a significant cybersecurity issue in the U.K. and other international locations affecting hospitals and healthcare information systems. We are also aware that there is evidence of this attack occurring inside the United States. We are working with our partners across government and in the private sector to develop a better understanding of the threat and to provide additional information on measures to protect your systems. We advise that you continue to exercise cybersecurity best practices - particularly with respect to email."
In another alert, the Department of Homeland Security's U.S. Computer Emergency Readiness Team says: "The WannaCry ransomware may be exploiting a vulnerability in Server Message Block 1.0 (SMBv1). For information on how to mitigate this vulnerability, review the US-CERT article on Microsoft SMBv1 Vulnerability and the Microsoft Security Bulletin MS17-010. Users and administrators are encouraged to review the US-CERT Alert TA16-091A to learn how to best protect against ransomware. "
Experts Warned This Would Happen
One security professional told Information Security Media Group that in the wake of the Equation Group SMB exploit coming to light, no organizations should have still been using unpatched Windows SMB and they should have eliminated all outdated or unpatchable systems that used it. Their failure to do so, this professional said, is evidenced by this ransomware worm now spreading.
Security experts have been predicting this type of outbreak would occur. On April 19, for example, U.K.-based security researcher Kevin Beaumont tweeted his prediction that the exploit would soon be targeted via a "ransomware worm" that would propagate around the world, encrypting as it went.
For any organization that isn't prepared, the U.K.-based security researcher known as Hacker Fantastic says that applying the patch to all systems should happen immediately and that all unpatchable systems should be immediately decommissioned and related firewall rules put in place.
How not to be hit by WCry 2.0: Apply MS17-010 immediately, remove NT4, 2000, XP-2003 from production, Firewall ports 445/139 & 3389. Simple.
As this attack unfolds - on a Friday, as such attacks inevitably seem to do - it's going to be a busy weekend for many information security professionals.
As organizations worldwide rush to mitigate the outbreak of the WannaCry crypto-locking ransomware, Adam Meyers of CrowdStrike shares insights on what researchers have gleaned from the attacks and how organizations should respond.
Meyers says initial indications are that healthcare organizations are being hit hard by WannaCry - but they are hardly alone."It seems to be a widespread campaign, so there's likely lots of different victims," Meyers says in a May 12 interview with Information Security Media Group. "We've seen indications that some of those victims are paying the ransom, and we've seen a couple thousand dollars, as of a few hours ago, transferred to the threat actors."
In an interview about the WannaCry outbreak (see audio link below photo), Meyers discusses:
What we know about the spread of the malware; What organizations can do - and should have done already - to mitigate their risks; The significance of this high-profile attack in the ecosystem of crimeware as a service.Meyers, vice president of intelligence at Crowdstrike, has over a decade of experience within the information security industry. He oversees CrowdStrike's intelligence gathering and cyber-adversarial monitoring activities. Before joining CrowdStrike, he was the director of cybersecurity intelligence at the national products and offerings division of SRA International.
Endpoint Security , Ransomware , Technology
Researcher Accidentally Blocks New Infections, But Warns Fix is Temporary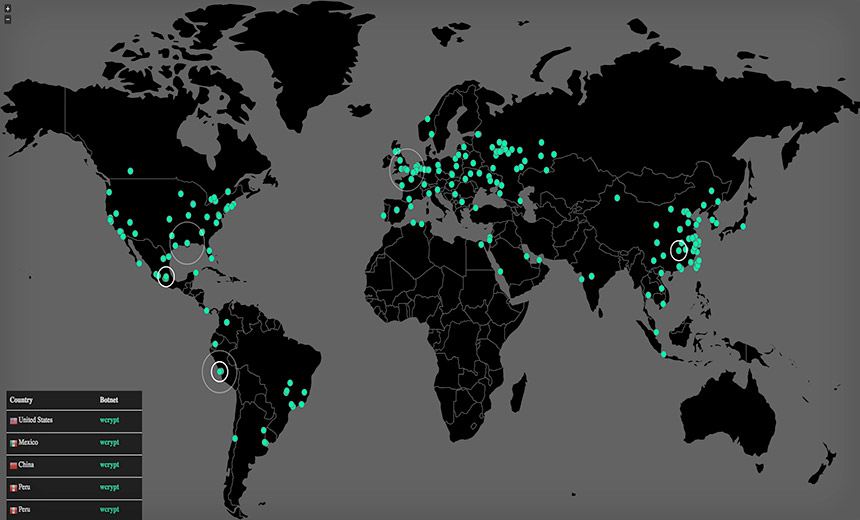 Sample of additional Wcrypt infections seen on May 13. (Source: MalwareTech)
Sample of additional Wcrypt infections seen on May 13. (Source: MalwareTech)Microsoft has issued emergency security updates for multiple operating systems that it no longer supports to help organizations protect themselves against a still-unfolding global cyber attack. The attack involves WannaCry crypto-locking ransomware, also known by various another names, including WCry and WanaCrypt0r.
See Also: Three and a Half Crimeware Trends to Watch in 2017
The ransomware is being spread via a worm that attempts to leverage two leaked exploits that have been tied to the National Security Agency, including one for an SMB flaw in all versions of Microsoft Windows XP to Server 2008 R2 (see WannaCry Ransomware Outbreak Spreads Worldwide).
Separately, a malware researcher appears to have found a "kill switch" for the strain of ransomware that has infected an estimated 75,000 endpoints in 100 countries. But the researcher warns that the respite is almost certainly temporary, since attackers could easily retool their code to enable their ransomware to once again forcibly encrypt infected PCs and hold them to ransom.
Related attacks unfolded May 12, and quickly compromised numerous organizations, ranging from Spanish telco Telefonica and numerous National Health Service trusts and doctor offices across England and Scotland, to Russia's interior ministry and the national rail network in Germany.
#WannaCry ransomware also hits German Train Station. pic.twitter.com/S5hIrsDe3G
The ransomware is being spread by a worm that targets a Windows SMB flaw. The flaw was patched by Microsoft in March via the MS17-010 security update, apparently after it was tipped off by the NSA. In April, the Shadow Brokers - a shadowy group believed to tie to the Russian government - leaked an exploit from the "Equation Group" - believed to be the National Security Agency's in-house hacking team, known as Tailored Access Operations - called EternalBlue that targeted the SMB flaw to then install a backdoor called DoublePulsar (see DoublePulsar Pwnage: Attackers Tap Equation Group Exploit).
Microsoft acknowledges in a blog post that it knows that some organizations and individuals still run versions of Windows that it no longer supports via issuing new security updates or other patches. "That means those customers will not have received the above mentioned security update released in March," according to a blog post from Microsoft's Trustworthy Computing team. "Given the potential impact to customers and their businesses, we made the decision to make the Security Update for platforms in custom support only, Windows XP, Windows 8, and Windows Server 2003, broadly available for download."
In addition, Microsoft said it added related signatures to its free Windows Defender anti-virus software. "Customers running anti-malware software from any number of security companies can confirm with their provider that they are protected," the company says.
Target: DoublePulsar, EternalBlue
Security firm Cisco Talos, in an analysis of the WannaCry attacks to date published May 12, says that the attack code is designed to look for the DoublePulsar backdoor, and if that's not found, to then try the EternalBlue exploit against an endpoint.
"WannaCry does not appear to be only be leveraging the EternalBlue modules associated with this attack framework, it is simply scanning accessible servers for the presence of the DoublePulsar backdoor," Cisco Talos security researchers write. "In cases where it identifies a host that has been implanted with this backdoor, it simply leverages the existing backdoor functionality available and uses it to infect the system with WannaCry."
Otherwise, attackers have programmed their attack code to target the SMB exploit. "In cases where the system has not been previously compromised and implanted with DoublePulsar, the malware will use EternalBlue for the initial exploitation of the SMB vulnerability," they write. "This is the cause of the worm-like activity that has been widely observed across the internet."
The attacks seen to date have demanded about $300 in bitcoins from victims to share an unlock code.
Bitcoin surveillance company Elliptic sys three different bitcoin wallet addresses have been hardcoded into the ransomware by attackers. But it's not clear if any ransomware victims have in fact received a working decryption key in response.
As of May 13, roughly 100 payments totaling 15 bitcoins - worth about $27,000 - had been sent to those bitcoin wallets.
But Elliptic has warned that the number of ransom payments may spike on May 15, three days after the initial infection. That's because the ransomware lock screen informs victims they have three days to pay, at which point the ransom demand doubles. After seven days, the malware warns, "you won't be able to recover your files forever."
'Accident' Disables Some New Attacks
A British security expert who goes by "Malware Tech" - and who declined to be named in press reports - told the BBC that he found a reference in the malware to a domain - www[.]iuqerfsodp9ifjaposdfjhgosurijfaewrwergwea[.]com - which wasn't registered. So he registered it.
MalwareTech tells the BBC how he accidentally disabled WannaCrypt infections seen to date.Only then, he found that the malware had been using the nonsense website name as a check: If the ransomware pinged that domain and received back a "domain not found" error message, the malware assumed that it was running on a legitimate endpoint. But if it received an "HTTP 200 OK answer," the malware assumed it was running in a virtual environment designed for studying malware, and the ransomware would then disable itself in an attempt to foil researchers.
MalwareTech says he has now redirected the domain name to a sinkhole which will redirect infected endpoints to instructions for how they can remove the attack code and patch their systems.
IP addresses from our sinkhole have been sent to FBI and ShadowServer so affected organizations should get a notification soon. patch ASAP.
"This sinkholed domain has prevented further infections occurring and has already resulted in preventing over 100,000 potential infections," the U.K. National Cyber Security Center, part of intelligence agency GCHQ, says in a blog post, noting that it's been working with MalwareTech. "However, this action will not remediate infections that have already occurred. Currently, the best mitigation available to prevent infection by Wannacry is the guidance presented in the following blog by MalwareTech and the latest ransomware guidance from the NCSC."
As of May 13, up to 200,000 endpoints appear to have been infected with the ransomware, according to MalwareTech. Any endpoint that was infected after MalwareTech sinkholed the domain referenced by the ransomware, however, will not be crypto-locked, at least with the current version of Wcrypt.
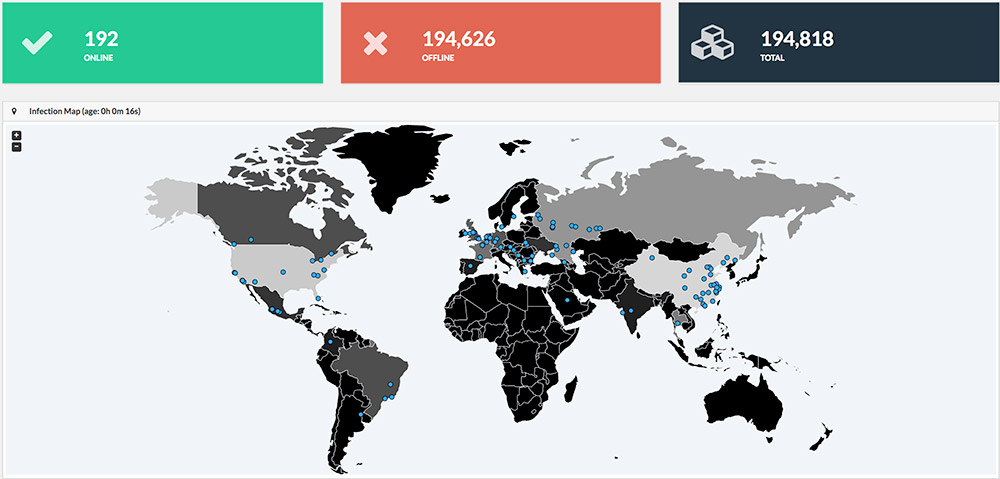 Wcrypt tracker shown on May 13. (Source: MalwareTech)
Wcrypt tracker shown on May 13. (Source: MalwareTech)Experts: No Surprise
Security experts say they are not surprised that this sort of attack unfolded, and they have been urging all organizations to install the MS17-010 security update as quickly as possible (see Responding to WannaCry Ransomware Outbreak).
"I think it was not if this was going to happen, it was really when," Professor Bill Buchanan at the Edinburgh Napier University School of Computing tells Sky News. "It's been well-known in the security community that this was a major, critical vulnerability that was announced on the 14th of March. So, industry has had over a month to be able to cope with this, and it's obvious that many systems haven't been patched. along with this, that many computers within the public sector are still running XP systems."
Cybersecurity expert Chris Pierson, CSO and general counsel for financial technology payment firm Viewpost, tells Information Security Media Group that it's also no surprise that mass attacks have affected the healthcare sector.
"Healthcare computers are usually always on, less frequently patched due to their role in the healthcare process, and oftentimes hospitals and clinics are lagging behind on cybersecurity controls," he says.
Respite Likely Brief; Mitigate Now
Security experts say that whoever is behind these attacks could easily learn from the mitigations that have been used against the code.
"It's very important that people patch their systems now because we did stop this one, but there will be another one coming and it will not be stoppable by us, " MalwareTech tells the BBC. "There's a lot of money in this, there's no reason for them to stop. There's not really much effort for them to change the code and then start over - so there's a good chance they are going to do it, maybe not this weekend but quite likely on Monday morning."
Alan Woodward, a professor of computer science at the University of Surrey who advises the EU's law enforcement intelligence agency, Europol, on cybersecurity matters, offered the following advice for all organizations: "Apply MS17-010. Isolate NT4, 2000, XP. Block ports 139, 445 and 3389."
For any organization that cannot apply MS17-010 or block those ports for some reason, "disable SMBv1," the NCSC recommends, pointing to related Microsoft guidance.
Some Microsoft customers have already still been paying for pricey "extended support" for Windows Server 2003 and Windows XP, which debuted more than 15 years ago. But Microsoft has been lauded by many security experts for stepping forward to issue emergency patches to the public.
"By releasing an out-of-bounds patch for unsupported operating systems such as Windows XP and Server 2003, people now are able to patch rather than having to attempt upgrades to newer system in order to be secured against this worm," says MalwareTech in a blog post.
Lynne Owens, head of the U.K. National Crime Agency, tells the BBC that no culprits or suspects have been identified behind the WannaCry outbreak, but that the agency has been deploying "all covert and overt means available to us" to try and track them down.
In Development
Receive Invite When Available
An analysis on rethinking where awareness programs fit in cyberdefense strategies leads the latest edition of the ISMG Security Report.
Also in the Security Report, you'll hear (click on player to listen):
The ISMG Security Report appears on this and other ISMG websites on Tuesdays and Fridays. Check out our May 5 and May 9 reports that respectively analyze then-FBI Director James Comey's testimony before the U.S. Congress on insiders posing a cyberthreat to the American law enforcement bureau, and the maturation of cybercrime.
The next ISMG Security Report will be posted on Tuesday, May 16.
Theme music for the ISMG Security Report is from Ithaca Audio under by Creative Commons license.

